I. Overview
This article refers to the address: http://
At present, there are many cases related to motor vehicles in various criminal offences, such as traffic accidents, escape and theft of motor vehicles. If an automatic monitoring point is set up on important roads and key sections of the urban area to realize 24-hour uninterrupted and all-weather automatic recording of passing vehicles, that is, installing a road vehicle monitoring and recording system, it can provide important clues for the public security department to detect cases. And the basis, and can effectively improve the management level of motor vehicles in the public security department. The construction of the “road smart bayonet†system is an indispensable means to create a safe road and realize road safety. It is also an important measure for the local public security traffic police department to create a “technical and strong police†demonstration city.
The road vehicle monitoring and recording system is developed using advanced optoelectronics, computer image processing, fuzzy recognition, and remote data access. The system continuously records the entire appearance (color, model, and license plate number) of each motor vehicle passing through the monitored road section in real time, and the system dynamically controls the captured vehicle image to capture the illegally driven vehicle. The information such as the time, speed and vehicle type of the vehicle through the bayonet monitoring point is generated and saved, and the information of each monitoring point is transmitted to the remote monitoring and command center through the broadband network to realize organic sharing.
This program is designed by Shanghai Anti-sales (China) Co., Ltd., a subsidiary of CSST Group, for the Shanghai Pudong New Area Urban Intelligent Monitoring System Project. It is based on the actual situation of the project, the site inspection of the company's engineering and technical personnel, and combined with the company for many years. Designed for practical experience in security monitoring.
Second, the technical design program
2.1 system composition
The system is divided into two parts: the intersection front-end monitoring system and the central management system, as shown in Figure 2-1. From the logical structure, it consists of four units, front-end camera and auxiliary lighting unit, image acquisition and processing unit, Transmission unit and central management unit.
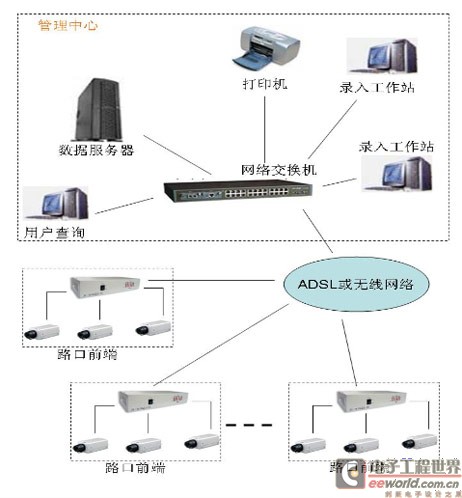
Figure 2-1 System structure diagram
2.2 front-end camera and auxiliary lighting unit
According to the actual situation of the road, the front-end camera uses 1/3''SonyEXviewCCD camera (the lens is automatic aperture, 18x optical zoom) to monitor the whole picture of the vehicle, called the panoramic camera. Within one lane of 3 lanes in one direction, one panoramic camera is installed in each direction, which is used to take panoramic photos of the front of the vehicle; in the case of single lanes or more, in order to obtain good picture effects, it is necessary to add a panoramic camera. Quantity. The cameras are mounted in an outdoor enclosure.
When the nighttime light is insufficient, a low-power CDM lamp or LED lamp is used as an auxiliary light source for illumination, and one or two auxiliary light sources are arranged per lane according to the scene lighting environment.
This program uses the infrared heavy-duty intelligent variable speed pan/tilt and camera of CSST's security sales company.
2.3 image acquisition and processing unit
The unit consists of a video server and corresponding control software. The control software includes image acquisition processing software and remote management software.
This program uses the video server of CSST's Security Sales (China) Co., Ltd.
2.4 transmission unit
The picture information is stored in the embedded DVR in the field, and the data will be recorded in the computer hard disk in a loop coverage manner. When it is necessary to query or recall the data, the broadband communication network needs to be used to transmit data, refer to Figure 2-4.
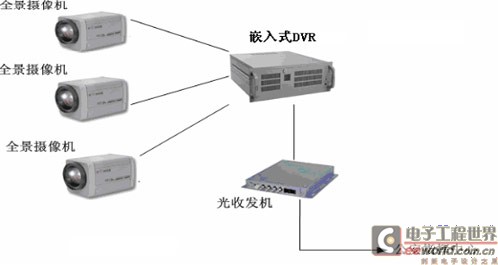
Figure 2-4 Schematic diagram of the front-end workstation at the intersection (on-site type)
Each of the above units constitutes a stand-alone system, that is, an intersection monitoring workstation, and each monitoring point needs to be installed at least one set.
2.5 Central Management Unit
In order to enable the command center to quickly obtain the alarm information of each front-end monitoring point, and play the function of centralized command and unified dispatching of the command center to improve the speed and accuracy of the police force deployment, it is necessary to establish a road vehicle monitoring system management platform. That is, a central data server is set up in the command center. The command center software consists of control software, data management software, and equipment monitoring software. Each user terminal has corresponding authority, which is an internal user in the public security network, and implements hierarchical management.
Third, the design description
3.1 front end configuration
3.1.1 front-end infrared heavy-duty intelligent variable speed pan/tilt head, camera unit
(1) Infrared heavy-duty intelligent variable speed pan/tilt
Infrared heavy-duty intelligent variable speed pan/tilt head of security sales company, all-weather environment design, high-strength aluminum alloy precision casting shell, anti-impact, anti-corrosion, protection grade IP66, with wiper function, strong wind resistance, stable and reliable operation, infrared night vision distance More than 100 meters, at night, the road surface of the monitored roadway is filled with light, and a picture of the vehicle with the same effect as the daytime can be obtained, as shown in the figure.
(2) color camera and lens
The camera uses a security sales company 1/2''ExviewHADCCD camera. Its horizontal resolution is 520, the minimum illumination is less than 0.01LUX, and it also has a strong light suppression function, which can eliminate the influence of the headlight illumination on the photo at night, so as to obtain a clear license plate number. The lens adopts the 8x (8mm-48mm) manual zoom lens of COMPUTAR of Japan, which is convenient for the best viewing range when installing and debugging.
3.1.2 Image Acquisition and Processing Unit
Image capture embedded DVR, the recorded panoramic image resolution is not lower than 768 × 576 pixels, the panoramic image should be able to see the vehicle type, number plate, color and contour and loading situation. According to the calculation of at least one panoramic image for each vehicle, images of at least 1.5 million vehicles can be stored, depending on the local traffic flow. Under normal circumstances, at least half a year of vehicle information can be stored. When the hard disk space is insufficient, the vehicle information and pictures with the earliest recording time are automatically covered.
3.1.3 transmission unit
This design does not design the transmission line, and the optical cable is provided by the user. To realize communication with the monitoring center, each monitoring point is designed to install a pair of optical transceivers (10/100M adaptive) or multi-channel video multiplexing optical transceivers.
3.1.4 Anti-interference and lightning protection
The system wiring adopts strong and weak electrical separation. A lightning rod is installed on the mounting bracket. The grounding resistance is less than 4 ohms. The camera is powered by 24v AC and equipped with a video lightning arrester.
3.2 Command Center
The road vehicle monitoring and management platform is a third-generation video and security management platform software for centralized monitoring and management of different types of digital image equipment and security alarm equipment in distributed monitoring places in large and medium-sized network environments. It is a fully digital, network-based and highly centralized platform. Managed next-generation security management platform software. It can centrally manage digital image devices and alarm devices such as on-site PC architecture DVR, embedded DVR, DVS and network camera. In addition to traditional network video surveillance functions, it increases central centralized configuration. Network-specific software such as real-time authentication, streaming media forwarding, centralized storage backup and WEB access, to build a complete large-scale network video and alarm management platform. Adopting advanced technologies and architectures such as J2EE, micro-core plus plug-in, WEBSERVICE, WEB2.0, O/RMAPPING, AOP, LDAP, SSO, etc., the software is more stable, secure, robust and open, and can meet the current postal savings monitoring across large and medium-sized regions. The needs of the network video and security monitoring field and the future integration into the industry's large information management system.
The platform software is different from the first generation digital monitoring management software, only has simple network sub-control management, and each security management system is independent of each other; it is also different from the second-generation centralized management software, although it realizes multi-system integrated network management, but the system The architecture is unstable, and the expansion of the industry's business needs is poor. The reason why the third-generation video and security management platform software is proposed is that the platform software should have all the basic security management functions of the second-generation software. A large number of advanced technologies and architectures such as J2EE, micro-core plus plug-ins, WEBSERVICE, WEB2.0, O/RMAPPING, AOP, LDAP, SSO, etc., which have been proven mature and reliable in the IT field, are compared with the previous security software. The system is more stable, secure, robust and open. The most important thing is that in the market environment where the current network monitoring customer needs are rapidly changing, it can quickly integrate the extended system functions with the business needs of the industry customers. It is the advanced technology of IT software development and traditional security security. The organic combination of management software. At present, some of the software has been successfully applied in China for more than several hundred million roads.
The large-scale network centralized monitoring and management platform includes application service software, C/S client and on-site PC architecture DVR software. The basic software of each specification is as follows:
(1) Application service software:
Manager system management server software: based on J2EE system and WebSERVICE standard, realize organization and role management and maintenance, realize centralized equipment configuration and maintenance management, combined with task plan execution and scheduling, alarm processing rule management, alarm acquisition and distribution management, electronic map concentration Configuration management, device inspection, and log management.
Web server software: Based on J2EE system and WebSERVICE standard, it provides unified WEB access configuration interface for system management, streaming media, alarm forwarding, centralized storage retrieval and other application servers, and provides unified remote monitoring and query WEB access interface for front-end monitoring equipment.
Medium Streaming Media Server Software: Used for client-side monitoring center multi-client multiplexing of the same live image streaming media forwarding management and on-site streaming media bandwidth limit management. The policy of limiting management includes the number of channels, user priority and event priority.
Storage network storage management server software: used in distributed and centralized storage environment, according to the plan and strategy set by the management center software to perform high-reliability image centralized storage, backup, retrieval and playback management.
Alarm alarm forwarding software: Under the central monitoring and management software settings, the device can quickly receive the alarm information of the field device and forward it to the designated central monitoring management software client, and can access the application service software running in the background. It provides alarm receiving and forwarding services, short message alarms, email alarms and other remote alarm services for all system-managed monitoring devices, and can access the short message alarm module.
Proxy video proxy server software: Provides unified information acquisition, transformation and proxy services for all embedded DVRs, facilitating unified interface management of the monitoring center.
(2) Dedicated C/S client software:
Monitort monitoring center main control software: mainly used for alarm, monitoring center main control workstation built-in program, can access all field devices under system management server authentication, can achieve round-robin preview, alarm alarm and alarm processing, electronic map and other functions. Support simple matrix decoder card output control.
Matrix network digital matrix software: mainly used to control the digital matrix control host built-in decoding card and matrix card arbitrary packet round-robin output, manual switching output and alarm linkage output, etc., support the coordination of other standard client soft decoding VGA output control.
(3) Field access server software:
DVRs digital hard disk recording system server software: PC-based, full-featured digital video recording and monitoring application software.
What is a wireless AC controller? What does it do?
Wireless AC controller is a kind of network device, such as the AC100/150 of Fengrunda, which can be used to centrally control and manage wireless aps. It is the core of a wireless network and is responsible for managing all wireless aps in the wireless network. AP management includes: delivering configuration, modifying related configuration parameters, RF intelligent management, and access security control.
Why use a wireless controller, and what exactly does it do?
In fact, the role of the wireless controller is to play a gateway function between the WLAN and the Internet (on the router), and the data from different access points are aggregated and accessed to the Internet. The role of an access point (AP) is to complete wireless access, and it can control user access through network flags.
The role of wireless controllers
1, Flexible networking mode and excellent scalability
The AP does not need to be directly connected to the AC, so that the AP can be deployed in any place that needs to be covered through the network, such as you deploy an AP in each employee's home, and then connect to the wireless controller inside the enterprise through the VPN, you can expand the wireless network of the enterprise to the family of each enterprise member.
2, intelligent RF management functions, automatic deployment and fault recovery
Through the dedicated RF management module, we can initially estimate the AP deployment according to the user's architectural design drawing, and can calculate the average bandwidth of the wireless terminal, the coverage between AP and AP in the actual debugging process.
3. Centralized network management
All the configuration of the wireless network can be completed by configuring the wireless controller. For example, enable, manage, and maintain all AP devices and mobile terminals, including all functions such as radio wave spectrum, wireless security, access authentication, mobile roaming, and access users.
4, powerful roaming function support
The wireless controller uses AP as the boundary combined with fast RF management system, which greatly reduces the connection time between wireless client and AP, and thus realizes the function of fast roaming.
5. Load balancing
AP and wireless controller systems can distribute wireless users or terminals to nearby aps within the coverage area of an AP, ensuring the number of each wireless terminal or the sum of AP bandwidth transmission or the upper limit of each wireless terminal bandwidth.
6, wireless terminal positioning, rapid fault location and intrusion detection
Wireless controllers can track and locate the location of wireless terminals, such as wirelessly connected computers, PDAs and Wi-Fi mobile phones.
7, powerful access and security policy control
At present, the wireless system supports authentication of 802.1, WEB authentication, MAC, SSID, VPN, etc., and supports various encryption modes such as WEP, WPA, WPA-PSK, WPA2, etc., and all configurations can be configured globally through the wireless controller.
8, Qos support
AP and wireless switching systems can limit the maximum bandwidth of a user's wireless connection within each user's privileges. For different IP services, the system can also define different QoS queues through the wireless switch module. For example, for wireless voice applications, SIP and RTP protocols can be set in the high queue, while common applications such as http and ftp can be set in the low queue.
The wireless controller AC is more advanced than the AP, plays the role of manager in the wireless network, and the wireless controller AC also acts as a client to complete a series of functions in the wired network (such as authentication, authentication, etc.). However, wireless controller AC is not a WLAN device specified in the 802.11 protocol family, but as a supplement to the protocol in specific applications, and its price far exceeds that of ordinary access point (AP) devices.
In small-scale wireless networks that use only a few aps, it is not economical to use expensive wireless controller AC equipment. However, if the number of wireless aps is large, more than 20 can be used AC controller.
Ac Controller,Gigabit Wlan Controller,Enterprise Ac Gateway,Wireless Ap Controller
Shenzhen MovingComm Technology Co., Ltd. , https://www.szmovingcomm.com
